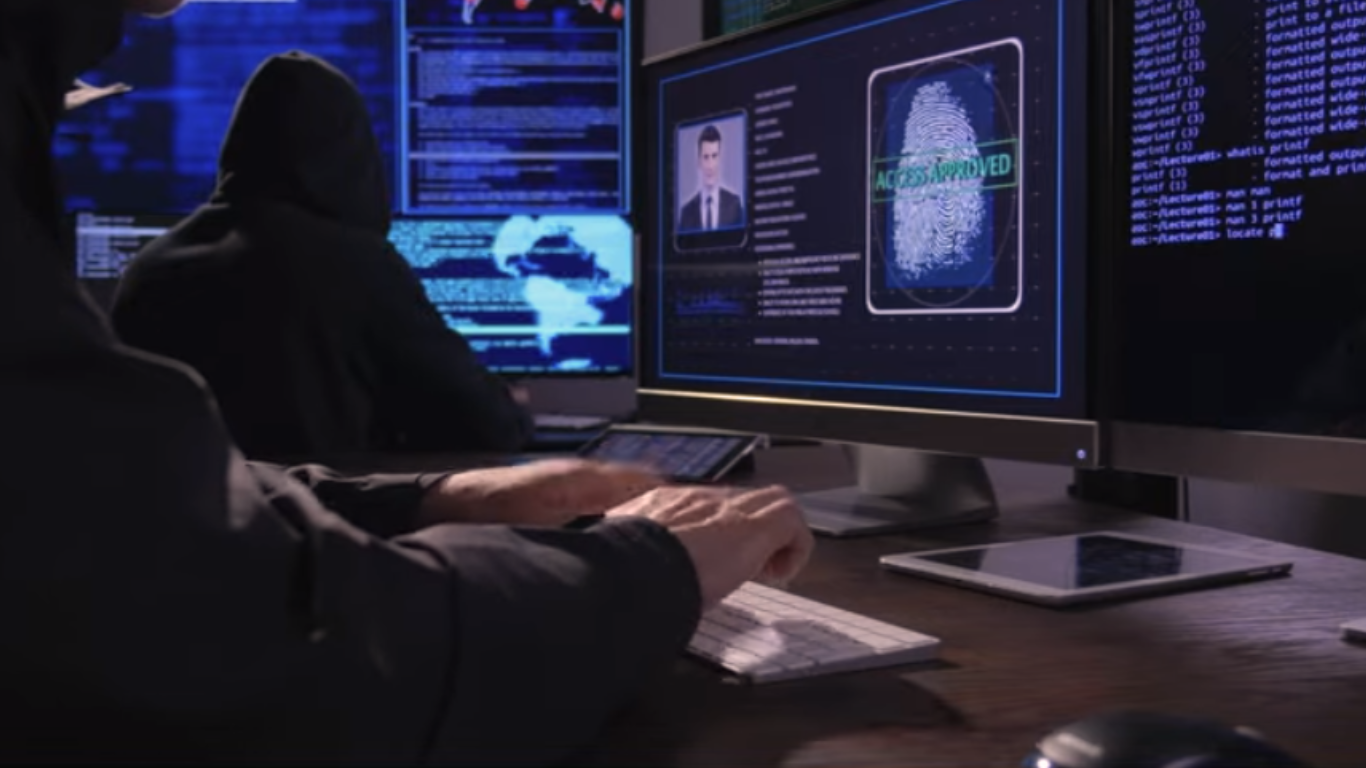
Top State-Sponsored Hacking Groups in 2026
If you think wars are only fought with tanks and missiles, you are already behind because in 2026, state-sponsored hacking groups are silently shaping global power from behind screens. Elite Cyber Units: The Most Dangerous State-Sponsored Hacking Groups of 2026: There is a strange shift happening in the world, and most people do not even … Read more